Malware & Monsters: Visual Guide
Malware & Monsters
Everything you need to play – read this before your first session
Two fully scripted zero-prep scenarios · 4–6 players + 1 IM · 45–75 min

First-Order Rules: The Only Things That Never Change
- The Core Loop: IM describes symptoms → each player takes one action → IM narrates results and advances the threat.
- Success Mechanic: Simple actions auto-succeed. Complex actions: roll d20. 5+ easy, 10+ medium, 15+ hard.
- Collaboration: +1 per assisting player (max +3), or roll two d20s and take the higher.
- The Goal: Contain the malmon using your roles before it evolves.
Everything else – modifiers, type effectiveness, degrees of success – is optional detail. The scenario teaches you each mechanic when it becomes relevant.
Pick Your Scenario (IM)
These are the two zero-prep scenarios in the IM Handbook, listed under IM Onboarding Scenarios in the sidebar. Both are fully scripted – every NPC line, clue, decision point, and resolution is written out.
| FakeBat: Friday Deadline | GaboonGrabber: The Fundraiser Email | |
|---|---|---|
| Setting | Creative agency, 12 employees | Nonprofit, 20 employees |
| Crisis | Malware on a machine, client deadline tomorrow | Credential theft, fundraiser in 48 hours |
| Best for | Technical teams | Mixed teams, first-timers |
Before the session (5 min): Open the FakeBat or GaboonGrabber facilitator guide. Print or have on screen. Bring role cards and Handouts A and B. One d20 per player.
What Is Malware & Monsters?
Malware & Monsters is a collaborative tabletop framework where a team of 4–6 security professionals investigates a realistic cyber incident, guided by one Incident Master (IM). Everyone else plays an IR role and investigates. No right answers are written in advance – only the constraints of real incident response: limited visibility, organizational pressure, and incomplete information. The team wins or loses together.
Every session is self-contained. No campaign prep, no continuity, no specialist rules knowledge required.
The Malmon Card
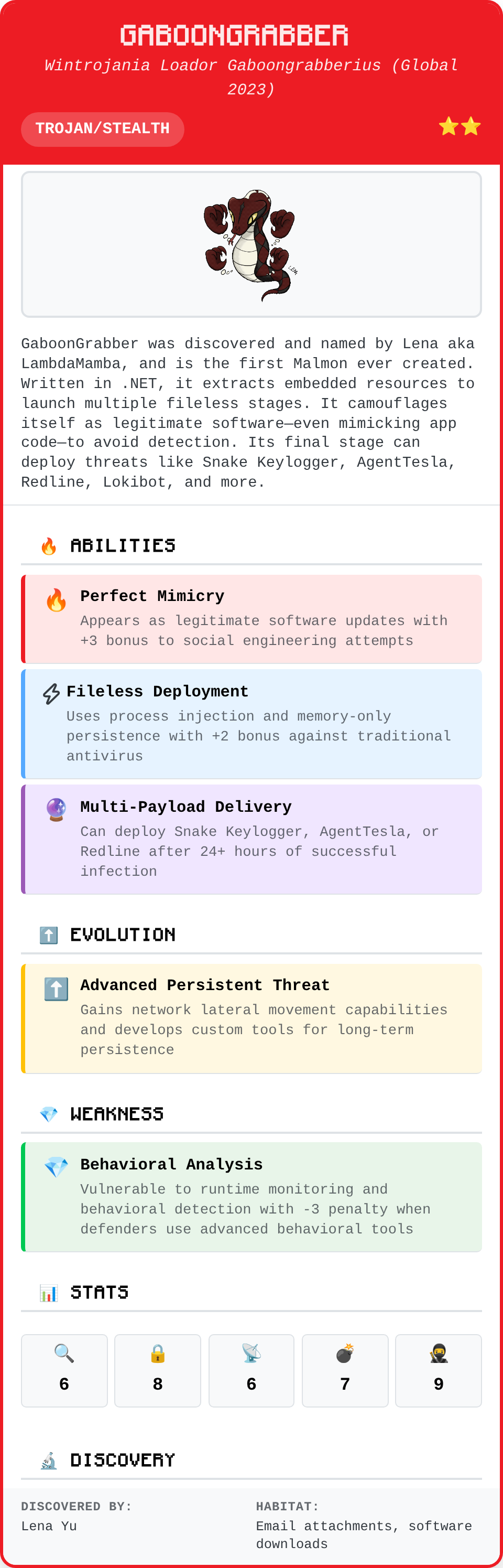
The malmon card is what the IM holds secretly – it defines the threat. Players never see it. The IM uses it to narrate symptoms, adjudicate actions, and decide when the threat escalates.
| Field | What it means |
|---|---|
| Name & Type | The threat identity and classification (Phishing, Ransomware, APT, etc.) |
| Stars | Difficulty rating – one star is a first-session malmon |
| Stats | Attack (how aggressive it escalates) and Stealth (how long before symptoms surface) |
| Abilities | The malmon’s signature tactics – what it does during the attack |
| Weakness | The approach that counters it – when to give the type bonus |
| Evolution Trigger | What the malmon achieves to escalate to Stage 2 |
| Discovery | The initial access vector – how it got in |
The Role Card
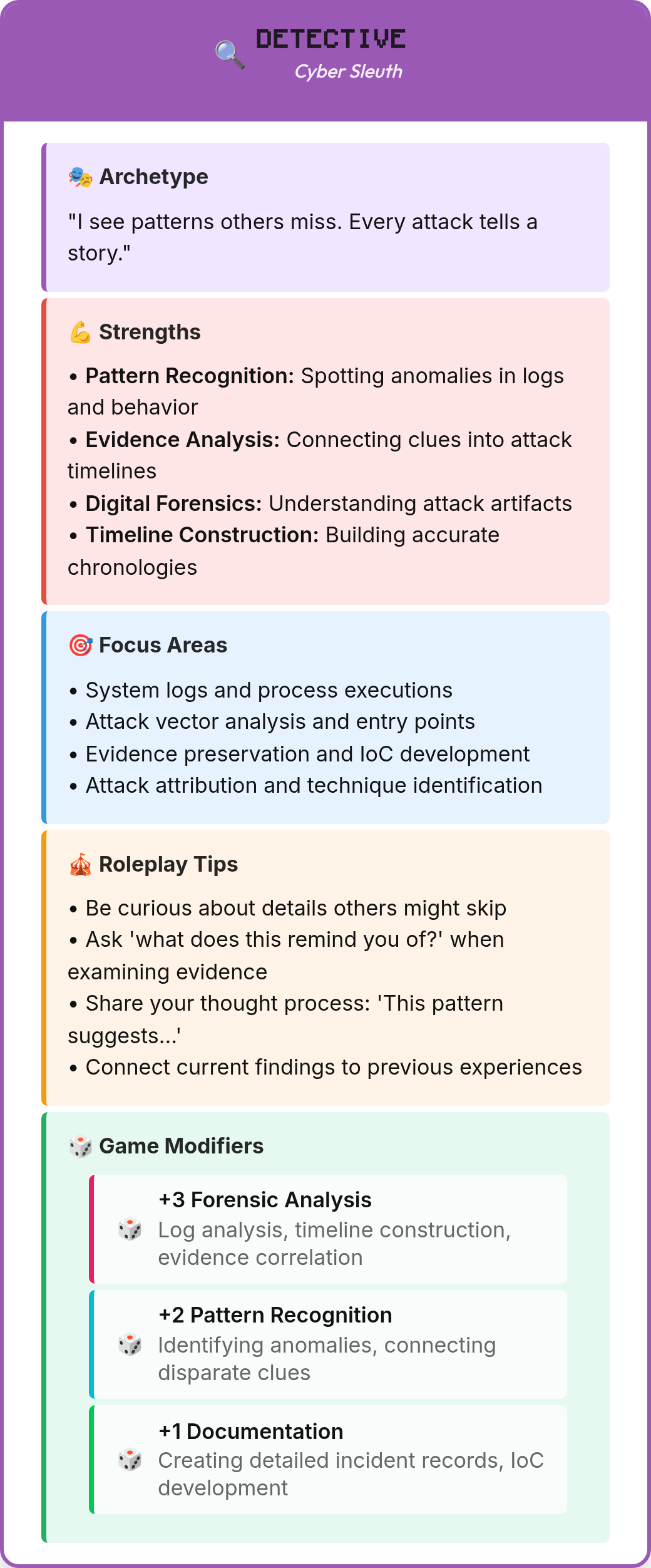
Each player holds one role card for the whole session. It tells you what you are good at, what questions to ask, and what modifier to add when actions match your expertise. You do not need to memorise it – just keep it in front of you and refer to it during play.
| Field | What it means |
|---|---|
| Archetype | Your investigative identity and mindset for the session |
| Strengths | Specific areas where you apply your +2 modifier |
| Focus Areas | The questions and tasks that belong to your role during play |
| Roleplay Tips | How to show up in discussion – not acting, just a behavioral frame |
| Game Modifiers | The exact bonuses and when they apply |
Setup
IM (5 minutes): Open the facilitator guide. Stack artifact handouts face-down. Keep the malmon card in front of you – players do not see it. You know the full picture from the start; everyone else discovers it through play.
Players (2 minutes): Open the Role Distributor on a phone or laptop. Enter headcount and tap Distribute. Each player opens their role card and places it face-up on the table. You are playing yourselves – no character acting required.
The 4 Core Roles
🔍 DETECTIVE
Find clues, connect evidence, build the timeline
🛡️ PROTECTOR
Contain the threat and keep systems running
📡 TRACKER
Watch the network, follow data flows, block exfiltration
📢 COMMUNICATOR
Coordinate people, translate impact, manage stakeholders
Fifth and sixth roles (Crisis Manager, Threat Hunter) suit complex scenarios with advanced malmons, multiple simultaneous threats, or other factors requiring more specialised coverage. Use the 4 core roles for your first session.
Playing the Game
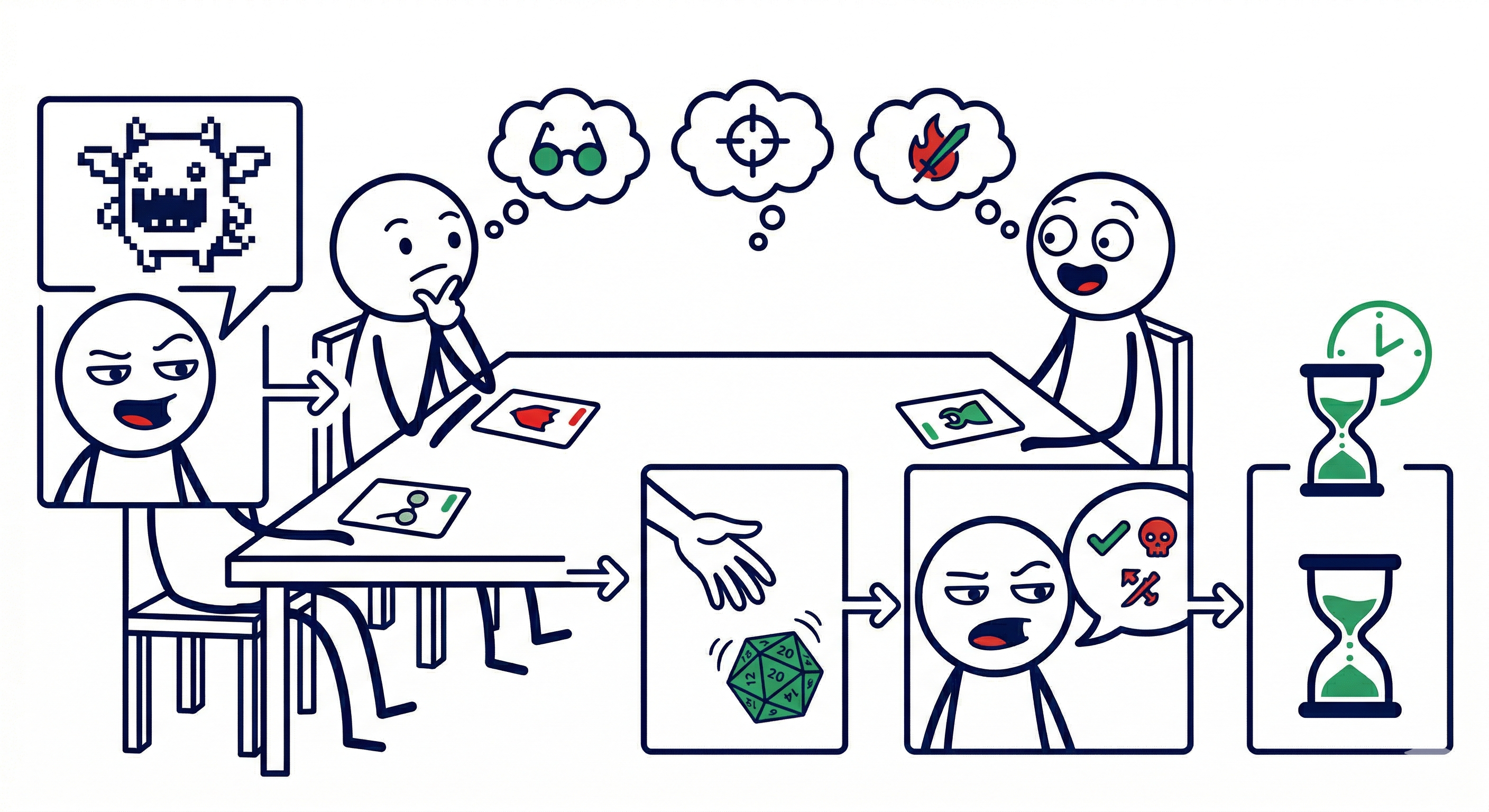
Every round follows the same sequence:
1. IM opens the round – describe what the team observes: alerts, NPC behaviour, system anomalies. Never name the malmon.
2. Players discuss freely – ask questions, form hypotheses, request information. The IM answers freely. This is free – no action, no roll. Most sessions are 70% discussion.
3. A player declares a specific action – “I want to analyse that log file” / “I call the finance director.” This costs your action. One per player per step.
4. IM judges the outcome – Clear expertise + right approach? Auto-success, no roll. Genuinely uncertain with real stakes? Proceed to step 5.
5. Roll d20 + modifiers – compare to target (5 / 10 / 15). Full success, partial (within 3), or failure.
6. IM narrates the result – deliver the next handout on a significant discovery. On failure: ask why – the answer is the learning moment.
7. Threat check – have the malmon’s evolution conditions been met? If yes, escalate and start Round 2.
Discussion is free. Actions cost your turn. Dice are rare.
The Roll
Only roll when the outcome is genuinely uncertain and failure would be interesting. Clear expertise + right approach = automatic success, no roll needed.
Difficulty
| Difficulty | Target | Success rate | Examples |
|---|---|---|---|
| Easy | 5+ | ~95% | Log review, standard comms, routine network scan |
| Medium | 10+ | ~70% | Malware analysis under pressure, coordinating a skeptical stakeholder |
| Hard | 15+ | ~40% | Cutting-edge analysis, high-stakes decisions with significant obstacles |
When in doubt, default to Medium. Step down if the player has hands-on expertise in exactly this situation – there is no need for a roll when the outcome is not genuinely in question.
With a +2 role modifier: ~100% / ~80% / ~55%.
Degrees of Success
| Result | When | What happens |
|---|---|---|
| Critical Success | Natural 20 | Exceptional result – bonus info, or advantage on next action |
| Full Success | Meets target | Action succeeds as intended |
| Partial Success | Within 3 below | Succeed with a complication, partial info, or a cost |
| Failure | 4+ below | Action fails; IM asks why |
A partial success is the most interesting result – something happened, but with a cost or complication the IM introduces. A failure is never a dead end: ask why the action failed, and that question is usually where the learning is.
Modifiers
| Source | Modifier |
|---|---|
| Action aligns with your role | +2 |
| Type advantage (super effective response) | +2 |
| Two players both contributed – both roll, take higher | advantage |
| Type weakness | –2 |
| Significant obstacle | –2 |
| Severe time pressure | –2 |
If a player’s real-world knowledge directly applies to the action they’re taking, that expertise is already a +2 – or skip the roll entirely if there is no genuine uncertainty.
Collaboration
+1 per assisting player (max +3), or advantage (roll two d20s, take the higher). When the whole team coordinates with clear role division, skip the dice – auto-success.
- Natural 20 – exceptional result: bonus information, or give the player advantage on their next action.
- Natural 1 – find the absurdist reading, not a punishment. Something slightly ridiculous happens and everyone moves on.
Session Structure
Three Rounds
- Round 1 – Discovery: What is happening? What systems are affected? Initial scope.
- Round 2 – Investigation: How did the attacker get in? What have they accessed? Full picture.
- Round 3 – Response: Contain the threat. Remediate. Communicate with stakeholders.
Injects
At key moments, hand the team a printed artifact handout. Players discuss how new evidence changes their picture. Deliver each inject after a significant discovery, after a decision point, or at the start of a new round.
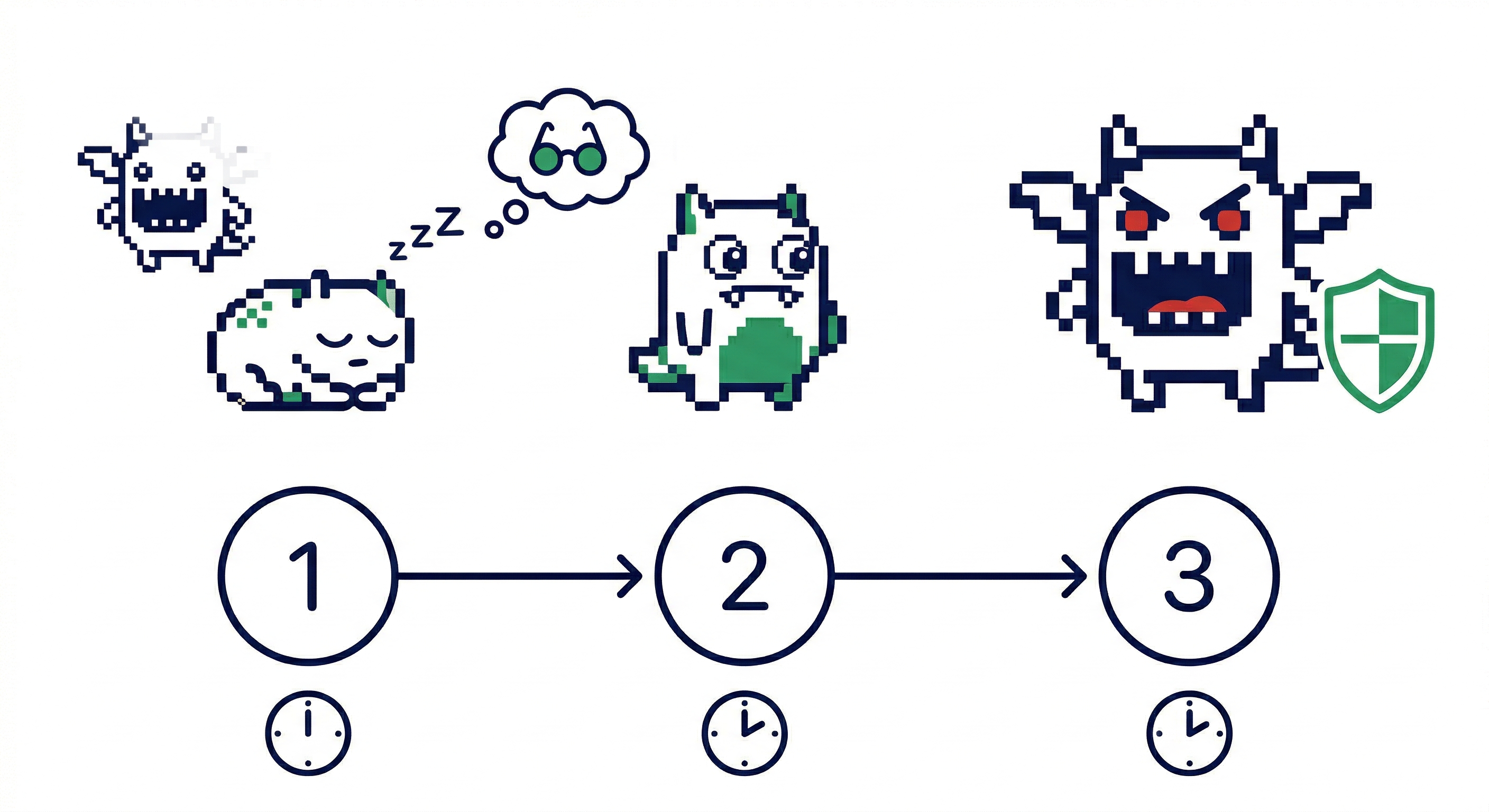
Evolution
When the team’s choices allow the threat to progress, the malmon evolves. Escalate stakes and deliver the next artifact handout. Evolution is not a punishment – it is the scenario advancing to its next phase.
Ending
Win: The malmon is contained before the threat escalates beyond recovery.
Lose: The threat reaches its Stage 2 objective – data exfiltrated, files compromised, client notified.
A loss in a hard scenario teaches more than an easy win.
Breaking the Rules
Malware & Monsters is made by hackers for hackers. So it’s only natural that it can be hacked. Use this fact to own M&M and make it your own.
The First-Order Rules are the only things that never change. Everything else is adjustable:
- Skip the dice entirely for groups where rolling feels artificial – narrate outcomes based on the quality of the team’s reasoning.
- Give advantage for a genuinely clever move – if a player makes a smart call that changes the room, let them roll twice and take the higher. Reserve it so it still means something.
- Let two players who both contributed both roll, take the higher. Faster than arbitrating who “gets” the roll, and teamwork should help.
- Don’t roll for facts, only for conclusions – real-world knowledge a player contributes counts without a roll. Roll when they’re drawing a conclusion under pressure, not when they’re contributing expertise.
- Let players name their own modifier – ask what skill they’re using. If they can justify it, give +2. It surfaces real expertise and makes specialisation feel earned.
- Roll your own dice when the world is undecided – if you haven’t decided whether something is true, roll out loud. The fiction breathes differently when even the IM doesn’t know yet.
- Adjust difficulty on the fly – if a group is struggling, drop targets by 3. If they’re coasting, raise them.
- Make nat 1s absurd, not punishing – find the ridiculous reading and move on. “With your nat one, you have estimated that the vibes are indeed bad.”
- Cut to Round 3 if time is short – pick a decision point and jump straight to containment and response.
Example Session: WannaCry
Advanced Scenario. Four players: Detective, Protector, Tracker, Communicator. Hospital under ransomware attack during flu season surge.
IM opens Round 1: “Tuesday evening. Memorial Health System – every ICU bed occupied, ED at 150% capacity. Network Admin Brian Martinez: ‘Thomas, I’m seeing automated SMB scanning on port 445 from dozens of internal addresses.’ ED Director Dr. Patricia Lee arrives seconds later: ‘Our systems are down. We have patients waiting and cannot access allergy records or lab results. This is a patient safety emergency.’”
Detective: “Are these systems patched? What OS?” IM: “Legacy Windows. The MS17-010 patch was deferred on medical device networks two months ago to avoid disrupting care.” Tracker: “I’m segmenting the clinical subnet from admin right now.” (Easy, target 5+. Rolls 14. Full success.) IM: “Clinical subnet isolated. Patient monitoring holds. But 14 ED workstations were already inside the propagation path – encrypted.”
Protector: “I check whether the malware queries any external domain before encrypting.” (Medium, target 10+, +2 role modifier. Rolls 6+2=8. Partial: 2 below target.) IM: “Incomplete firewall logs. You catch outbound DNS queries to a long randomised domain, but can’t confirm what it does.” Communicator: “I get Microsoft support on the phone and read them the domain.” (Medium, target 10+, +2 role modifier. Rolls 11+2=13. Full success.) IM: “It’s the WannaCry kill switch – registered by a researcher during the 2017 outbreak. You push the entry to your resolver. Propagation stops.”
The Protector’s partial success left just enough for the Communicator to act on. Neither alone would have got there.
IM – full picture: “Here is what the IM knew from the start. Memorial Health deferred the MS17-010 patch two months ago to protect medical device uptime – a reasonable operational call with serious consequences. WannaCry exploited EternalBlue, spread automatically across every unpatched host, and encrypted 14 administrative workstations. Network segmentation was incomplete; the Tracker’s fast containment closed that gap before ICU monitoring fell. The kill switch halted further propagation. Patient care restored within four hours.”
The team kept the ICU online. That is incident response.
That is one way it plays out. What would your team have done at the segmentation call?
Find out at malwareandmonsters.com
Resources
All resources at malwareandmonsters.com
| Resource | What it’s for |
|---|---|
| FakeBat: Friday Deadline | Scripted facilitator guide – NPC lines, clues, resolution |
| GaboonGrabber: The Fundraiser Email | Scripted facilitator guide – NPC lines, clues, resolution |
| Role Distributor | Assign roles to players in seconds |
| Printable Tent Cards | A4 folded cards – one per player seat |
| Players Quick Start | One-page player onboarding |
| IM Quick Start Guide | Full IM reference including all mechanics |
Malmons aka Malware Monsters © 2025 Lena Yu aka LambdaMamba. All rights reserved.